Auth.GNU
From Linuxnetworks
Contents
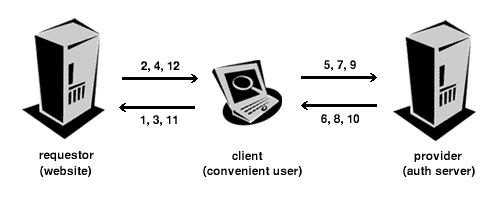
Proposal for a possible Auth.GNU architecture
First time
- Request for content to a web site by an user
- Request for resource locator by the web site
- Reply with resource locator by the user
- Redirect to resource location + requested auth information
- Request for auth information to the auth provider by the web site over the client
- Request for auth by the authentication provider
- Reply to auth request by the user
- Request if transmission of the requested data is ok
- Reply to transmission request with policy
- Redirect to web site based on policy with requested information
- Reply to web site with auth information over the client
- Reply of web site with requested content
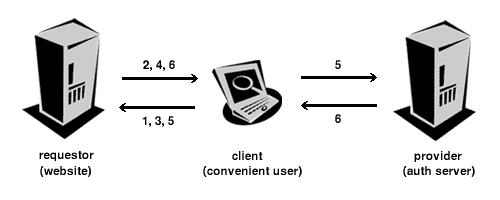
Other times
- Request for content to a web site by an user
- Request for resource locator by the web site
- Reply with resource locator by the user
- Redirect to resource location + requested auth information
- Request for auth information to the auth provider by the web site over the client
- Redirect to web site based on policy with requested information
- Reply to web site with auth information over the client
- Reply of web site with requested content
Advantages
- Based on the HTTP protocol
- Resource locator consists of a HTTP address with a username
- Easy extensibe through embedded XML Auth.GNU protocol (show me anything I can't handle :-) )
- Nothing have to be installed on the client
- Server administrator is not involved
- Easy for the web site creator
- User can have several identities based on the web site URL
- User can use several auth provider based on the resource locator
Disadvantages
- User have to trust auth provider through the lack of encryption
- User must insert the resource locator every time, if auto fill of forms is disabled
- Screen may flicker through redirects
Possible extensions
- Creation of a browser plugin, which encrypts and decrypts transfered data locally
- Plugin can handle different ways of authentication to auth provider (password, smart card, etc)
- Plugin can be invoked by web site to reply the resource locator without user interaction